Sophisticated Types of Ransomware Attack Found Lurking Online




 (1 votes, average: 5.00 out of 5)
(1 votes, average: 5.00 out of 5)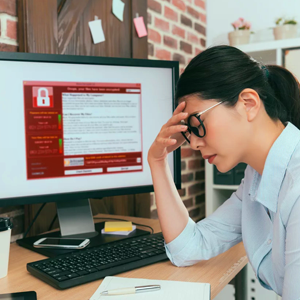 The new versions of ransomware are lurking on the Internet. Learn how these new types of ransomware work to avoid falling victim to a ransom attack.
The new versions of ransomware are lurking on the Internet. Learn how these new types of ransomware work to avoid falling victim to a ransom attack.
- TrumpHead Ransomware
The TrumpHead ransomware was discovered on January 14, 2018, pretending as a fake PDF or freeware. To carry out a ransom attack, TrumpHead ransomware deletes the shadow copy of the OS that allows the user to recover the file through backup. Once the file encryption process is finished, TrumpHead ransomware leaves a note within the encrypted files entitled READ_THIS.html that contains the instructions for paying the ransom. - Djvu Ransomware
The Djvu ransomware is the new member of STOP ransomware that warrants paying the ransom after performing a ransom attack. It is distributed through a fake copy of the software. Once installed, the Djvu ransomware adds any of these extensions to the filename .djvu, pdff, and the latest extension, .tro. As of today, Djvu ransomware remains undecryptable, making it impossible to recover ransomware encrypted through third party software. - BlackRouter Ransomware
The BlackRouter ransomware works alongside another ransomware called Black Heart. The latter installs remote access software called AnyDesk which contains BlackRouter ransomware. While AnyDesk is installing, BlackRouter starts encrypting files in the hard drive. The hacker demands $50 per encrypted file.That’s how the BlackRouter ransomware carries out a ransom attack. - Xcry Ransomware
The Xcry ransomware is installed through system vulnerabilities. Once installed on the computer, the Xcry virus carries out a ransom attack by locking various types of documents using AES encryption cryptography. The hacker can be reached at funnybtc@airmail.cc, if the user decides to pay to recover ransomware encrypted files. - Obfuscated Ransomware
The newly discovered ransomware called Obfuscated adds “.obfuscated” extension to the filename once the encryption process is completed. The user is advised to contact the hacker at bigbobross@protonmail.com and pay for the decryption key in Bitcoin to restore the files. Paying the ransom is a bad idea, because not all hackers will provide the decryption keys once they receive the ransom. So the victim is at risk of losing money and files at the same time. However, falling victim to a ransom attack is preventable. If the users take precaution, they will avoid becoming a victim of ransomware.
So what can you do to prevent a ransom attack?
- Use a Strong Password
Hackers today use brute-force to crack a password with the help of software that auto-generates password. If your password is weak, hackers can easily crack it and install ransomware on your device. Use a strong password that consists of upper case letters, numbers, and special characters. The combination makes the password difficult to crack. - Update the Software
Hackers commonly distribute ransomware through a system vulnerability. It is the result of a coding error. A software update is designed to fix system vulnerabilities. So when the user fails to install a patch, the computer becomes vulnerable to a ransom attack. - Install a Reputable Security Software
A security software is designed to combat varieties of malware such as ransomware. It protects the computer against unauthorized access, so a hacker can never gain control over the computer if you have the best security installed on your computer. Install a security software that provides the best ransomware protection such as Xcitium Advanced Endpoint Protection.
What is Xcitium Advanced Endpoint Protection?
Xcitium Advanced Endpoint Protection is unlike the traditional security software. It is an advanced software designed to protect the network and endpoint devices against sophisticated types of malware. It has multi-layered security that prevent the entry of malware.
Once a malware reaches the computer, it is countered by Xcitium antivirus that instantly detects and blocks malware. The antivirus is cloud-based, so even if the user doesn’t have the latest version of the software, it will be able to detect new threats.
Xcitium Advanced Endpoint Protection is also equipped with a fileless malware defense system called HIPS or Host Intrusion Prevention System. So when fileless malware such as VBScript or Powershell enters the computer, it is immediately identified and blocked. HIPS is constantly monitoring the computer memory and registry which the fileless malware targets to evade the detection of the anti malware software.
Through the Auto-Containment technology built on Default-Deny, Xcitium Advanced Endpoint Protection prevents malware infections brought about by any untrusted file. It never permits any file to run in the computer until it is verified as safe. It executes the file within a virtual container then decides whether to eliminate or release it depending on the verdict.
Even if sophisticated ransomware are lurking on the Internet, if you have the best security software installed on the computer, you’ll avoid becoming a victim of a ransom attack. Download Xcitium Advanced Endpoint Protection now.