Trojan Horse




 (1 votes, average: 5.00 out of 5)
(1 votes, average: 5.00 out of 5)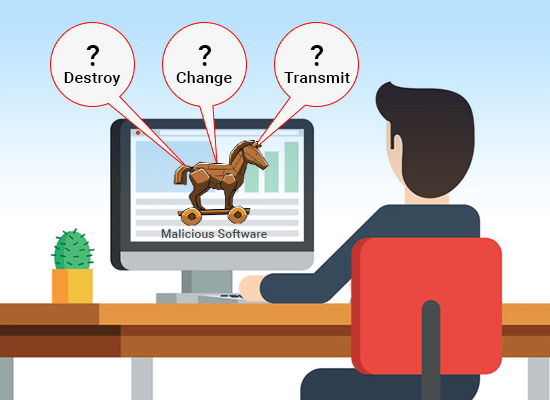 The Trojan horse got its name from the a story about the Greek soldiers. The Greeks soldiers deceived the Trojans by presenting a giant wooden horse. That’s what the malicious program, Trojan horse, does as well. It disguises itself as a regular file that you wouldn’t even notice. Thus, it might take a while before you notice the threat it brought to your endpoint.
The Trojan horse got its name from the a story about the Greek soldiers. The Greeks soldiers deceived the Trojans by presenting a giant wooden horse. That’s what the malicious program, Trojan horse, does as well. It disguises itself as a regular file that you wouldn’t even notice. Thus, it might take a while before you notice the threat it brought to your endpoint.
A Trojan horse is a type of malware – not a virus. The Trojan horse virus can replicate itself while the Trojan horse can’t do that. This is the very reason why many cyber criminals use a various methods and tricks to delude users to install a Trojan into their endpoint. When it’s successfully installed onto the endpoint, it can perform any task the attacker designed to do.
How does Trojan Horse work?
Of course, it’s important to know how to know how a Trojan horse acts once its on your endpoint. For that, a scenario will be given for clearer illustration of how a Trojan works:
It will all start when the victim receives an authentic-looking email with an attachment. The attachment surely carries a malicious code that will be activated when the victim downloads the attachment. Most of the time, the Trojan won’t be detectable. The computer will continue working as usual, yet it’s already infected with a Trojan horse.
The Trojan stays undetected until a specific date. Or until the victim carries out a specific action, such as visiting an online banking website. At that time, the trigger activates the malicious code and carries out its intended action. The Trojan can also be made to delete itself after it has done its intended function. It may return to a dormant state or it may continue to be active.
How to Identify Trojan Horse?
You might think that it’s easy to delete a Trojan Horse. That’s the hard part; it looks like any other ordinary file such as a photo editing software, an antivirus, or even an MP3 song. A Trojan horse can take any form of file because it’s crafted to trick the endpoint users.
Reformatting your endpoint might be the answer on your mind, but you’ll definitely lose all of your important files. Heartbreaking, isn’t it? After collecting all the files you’ve worked hard for, you just have to decide which one is harmful.
The cyber criminals use the method called social engineering to work against you. They’ll use deceitful language to convince you that the Trojan horse is a authentic app or program. When you install the Trojan horse, it’ll definitely work to do malicious activities on your endpoint.
What does the Trojan Horse do?
The Trojan horse is one of the most used malware by cyber criminals. It can go unnoticed for a long time that it’s almost a jackpot once successfully installed into an endpoint. Remember the following abilities of a Trojan for better security planning:
Spying
Trojans can work as a Spyware. It’ll wait until you use your online accounts or enter your credit card details. Then, it’ll send your passwords and other information back to the cyber criminal.
Creating backdoor
Trojans also has the ability to change your codes or your security system. With that, even more malware can get through your security tools without getting noticed.
Send expensive SMS messages
If you’re surprised by a huge increase in your phone bill, you might want to check your smartphone too. Endpoints aren’t the only targets of Trojans. It can also use smartphones to send expensive SMS messages to premium numbers. A cyber criminal can make money through that.
Turn your endpoint into a zombie!
Cyber criminal don’t steal accounts or information. They also pester other people using Distributed Denial of Service (DDoS) attacks. DDoS attacks aim to overload the server with traffic from multiple origins. In order to do that, they’ll implant Trojans to endpoint and use it for their own interest. That will put you in great trouble as cyber crimes are detected through IP addresses of the endpoint.
Xcitium Antivirus Resources