How to deal with lock screen ransomware




 (2 votes, average: 5.00 out of 5)
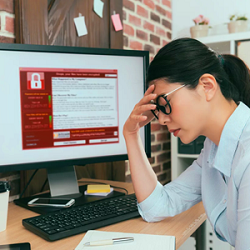
(2 votes, average: 5.00 out of 5)Lock screen ransomware, also known as lockware, is one of the three main forms of ransomware in common use today. Although it can look intimidating, it’s actually very easy to remove it. Here is a quick guide on how to deal with lock screen ransomware and the other common forms of ransomware.
Lock screen ransomware (and scareware)
Lockware is really a twist on a form of ransomware commonly known as scareware. As its name suggests, scareware is a very basic form of ransomware. It simply displays a threatening message on the victim’s screen and hopes that this will intimidate them into paying the attacker. Dealing with scareware generally just means installing a reputable anti-malware program and having it scan your computer.
Lockware, however, takes this tactic a step further. It really does lock your computer so you can’t use it. The lock, however, is very easy to bypass if you just keep calm. This means that, as with scareware, the real power of lockware is its ability to create fear.
Lockware, however, takes this tactic a step further. It really does lock your computer so you can’t use it. The lock, however, is very easy to bypass if you just keep calm. This means that, as with scareware, the real power of lockware is its ability to create fear.
The way to deal with it is to boot into safe mode. If possible, just install a reputable anti-malware program and have it scan your computer. If that is not possible, restore to a previous time point (before the infection) and then install a reputable anti-malware program and have it scan your computer.
Encryption ransomware
These days, encryption ransomware is often what people mean when they just say “ransomware”. This is probably because it is now the type of ransomware that is most likely to hit the headlines. It is also the type of ransomware people tend to fear most since it can literally cause businesses to collapse if you fail to protect yourself effectively. The irony of this situation is that, with effective preparation, encryption ransomware can become nothing more than a minor inconvenience.
Protecting yourself in the event of an encryption ransomware attack
When it comes to encryption ransomware, you need to work on the assumption that your defenses are going to be breached. This means that you need to think about how to make sure that your data is protected even if a third party accesses your production system.
Step one is to ensure that all your sensitive data is kept encrypted. If that sounds like too big a task then, at the very least, make sure that all personally identifiable data is kept encrypted. This won’t stop an encryption Ransomware attacks. It will, however, mean that they cannot use the data for anything other than ransom. In particular, they won’t be able to sell it or expose it (if you refuse to pay the ransom). This means that you will stay on the right side of data protection laws.
Step two is to make sure that you have a ransomware-proof approach to data backup. Here, the key point to understand is that any attack which can breach a production system can, at least potentially, breach a local data backup. In the case of ransomware attacks, this is particularly likely if you are running automated data backups.
The way to deal with this is to make sure that you also have an off-site data backup. This needs to be both physically and logically separate from your main system. Ideally, it should contain backups from different time points in case there is a delay in recognizing that you’ve been compromised. If you’re in the cloud, then you can reduce the cost of this by moving backups into slower storage as they age.
Preventing ransomware attacks
On the one hand, there’s nothing that can guarantee you 100% protection from ransomware (or any other kind of malware). On the other hand, there’s nothing to stop you from trying your best and you should certainly aim to do so. Apart from anything else, the more ransomware attacks you can stop, the less downtime you’ll be likely to experience as you restore from a backup.
Your main defense against ransomware is a proper anti-malware program with an integrated firewall, backed by a reputable cybersecurity company. Getting an anti-malware option with an integrated firewall gives you complete protection (almost) out of the box. There should be minimal configuration necessary. As a bonus, this tends to be the most cost-effective option.
These days, the best solutions tend to be cloud-based. This is partly because cloud-based solutions can be updated more quickly than locally-installed apps. It’s also partly because the main processing and storage load goes onto the back-end servers rather than the local machines.
You also need to make sure that you only use operating systems and locally-installed applications which are still supported by their developers and that all updates are applied promptly.
Please click now to start your free 30-day trial of Xcitium AEP.
Related Sources:
Endpoint Detection
Endpoint Detection and Response
Ransomware And Law
Ransomware Protection
Ransomware Removal
Ransomware Virus
Equipment Inventory Software
Cyber Security Protection Against Ransomware