VALKYRIE




 (6 votes, average: 3.83 out of 5)
(6 votes, average: 3.83 out of 5)Valkyrie is a cloud based file analysis platform providing static, dynamic and even human expert analysis for submitted known and unknown files, providing the file analysis platform for all Xcitium 360 solutions. Valkyrie’s verdict driven, file analysis platform, processes over 200 million unknown file submissions each day, uncovering more than 300 million unknown files every year – through tightly integrated Xcitium solutions, partnerships and our active global community of threat researchers.
INTEGRATIONS
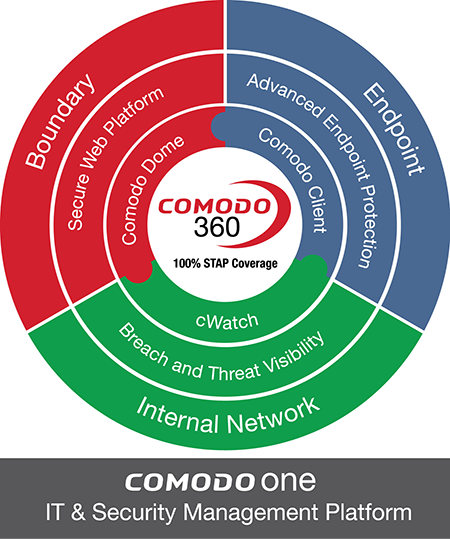
Valkyrie is tightly integrated into the Xcitium 360 platform, providing file analysis for Xcitium Advanced Endpoint, Network and Boundary solutions. This tight integration provides the essential file analysis needed to provide real-time file decisions.
ADVANCED ENDPOINT PROTECTION
Within Xcitium’s Advanced Endpoint Protection solution is Xcitium Client, a next generation endpoint client which provides a multi-layered approach to endpoint security. As part of this multi-layered approach, Xcitium Client can be configured to work directly with Valkyrie. This tight communication between Xcitium Client and Valkyrie allows Xcitium Client to stay constantly updated with the known good and the known bad, leaving only unknown files which Xcitium client automatically contains, using Xcitium’s lightweight, patent-pending container. While that unknown file is contained, Xcitium Client automatically sends that file for analysis. This direct communication of unknown files ensures that unknown files run in containment for the shortest time possible.
Xcitium DOME SECURE WEB PLATFORM
Xcitium Dome offers a modular approach to securing the network boundary, with service offerings such as Advanced Threat Protection, Web Security, Bandwidth Management, Portable Containment and many others. Valkyrie integrations provide the foundation of many of these services; in particular, Portable Containment utilizes Valkyrie’s file intelligence to analyze files while they are in transit, allowing the known good, blocking the known bad and employing Xcitium’s portable containment technology on the unknown. This portable containment wraps the unknown file in a lightweight container that is transmitted to the receiving endpoint. This “wrapped” file can then be run on the receiving endpoint without the risk of infection, even on completely unprotected endpoints.
CWATCH BREACH PREVENTION AND COMPLIANCE
cWatch offers a modular self-managed or true Security-as-a-Service platform for advanced breach prevention and threat monitoring. cWatch’s modular design allows for flexible deployment of network sensors, allowing for in-depth monitoring for every aspect of your environment. This security information is then analyzed by Xcitium’s expert security personnel and combined with the advanced file analysis provided by Valkyrie. This tight integration into Valkyrie provides Xcitium’s security experts with the entire wealth of information contained in Valkyrie and provides the big data analytics that are essential for exploit validation and response.
RESEARCH PARTNERS
Valkyrie provides a powerful research platform for malware researchers, partners or anyone interested in malware research. Novice users can upload files directly to Valkyrie through its website, while more advanced interactions can be constructed via plug-ins and RestAPI web services.
Related Resources